Phishing as a Modern Way of Victimizing.
Within this post you will enjoy your internet vocabulary with new notions. So, let’s talk about PHISHING.
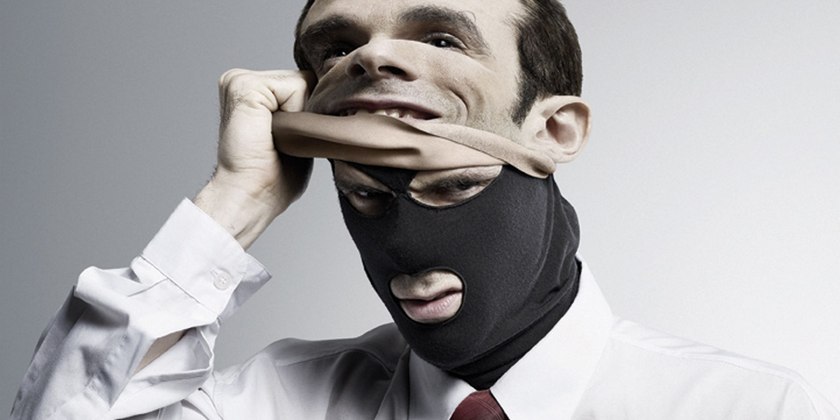
Internet crimes develop step in step with modern technologies and anyone who has a device with the internet connection can be affected at any time. Typical phishing scams under the false identity of a legitimate organization try to lure out personal information or entice people into installing malware and spyware onto their devices, with this giving full access to stored files, account passwords, bank account numbers or other sensitive data. Awareness of modern ways of victimizing and knowing what to do to protect yourself and people around you from fraud and scam are important in preventing hackers or phishers to exploit your vulnerabilities.

If we imagine a fish, there is a fisherman somewhere next to her dreaming about a good game!
Modern life dictates new rules of surviving and the internet can lead to a lot of income or a loss. For now, we mean the process of activities of a group of people who represent a “trustworthy entity” in the sphere of electronic communication.
The aim is to obtain secret information (logins, PIN numbers, etc.) from social websites and online payment processors via spam mailing. Such messages have links. Or there are forms that ask to write your data. A letter usually makes a user enter his personal details on the website looks like a legitimate one, real and with a good reputation (good job!). All these data are to be used for different purposes, of course.
To Each Other Known From Afar All Of The Fishermen Are
Let us say that such ascension of this way of earning money with malware disquiet us and tends to become striking fraud of 21 century. Educated and smart people can create powerful groups that are difficult to disclose or neutralize.
Each year the number of reported fishing incidents grows, nevertheless, good attempts to deal with them are to be taken regularly.

So we will try to give you the proper advice how to be attentive with all of that.
- First of all, always check letters in your mailbox. Usually, such messages commonly come from legitimate organizations as a bank, government agency, retailer, etc. You get an email with congratulations because you have won a prize and the company needs some information about you. Of course, you will be happy and you will imagine this prize and how lucky you are. They have sent you the email with a form where you need to write some details. Now you know why they need this and what you should do!
- Did you get the links in your email? Check the link and the website. Profit! To check if the company is real – use any search engine by investigating their website or you may call them if you find any phone number. Such a “real agency” intends to pay attention to the main subject. But what about the details? As a rule, people react surprisingly fast without thinking. That is why if you stop for a moment and analyze, probably you won’t find any characteristic of a real organization.
- The most modern and powerful online ID theft is called “pharming”. They work when you use your browser. So you wish to enter the website and you need to use your login and password for entering. Check where you do this! This is the way they get data.
- Ok. Pop-up screen. Please remember: real legitimate organizations ask to confirm your data another way. Such a system is often used to get data when you are browsing.
- Do not ignore anti-virus and anti-spyware software, never forget about spam filters and a firewall. Watch them be always updated. Note that your mailbox settings system is smart enough and offers you have a spam filter. Software that protects your data should scan messages you get. Let your anti-spyware software look for programs you installed. Firewalls secure your computer from unauthorized phishing attacks.
- When receive emails with attachments, open those ones you are sure in the safety of its content (if you know exactly or expect). At first you think that you get a letter from someone you know. However, that’s the first impression.
- Phone phishing. You get a call from a company representative who needs more information about you.
- Warning message signifying that you have been a victim of fraud. In this case, verify this information carefully as well as identify the person you receive such a claim from. Trustworthy legal organizations keep all information carefully. They don’t need to request for personal or billing information. Anyway, our general advice is to find the proper number and try to contact you directly to investigate the issue.
- When you are looking for a job – be attentive with job search websites. Keep your data private.
- Make sure who is writing. Do you know him or her? Sometimes you may think that you get an email from a famous person.
- After providing any information to a phisher – each minute is important. Contact fast the companies where you have accounts to tell about this case. Report about your victimizing in detail. That will help to fix the issue.
Remember: choose serious companies, the ones that behave differently. Use your time carefully and never regret: you will not waste it, you will spend it for saving your money and reputation.
